The dark web whispers with its allure of anonymity and untamed territory. For those brave enough to venture, the encrypted networks known as Onionlinks offer a glimpse into a dimension beyond the surface web's grasp. But navigating this labyrinth requires a sharp mind and a willingness to decode its secrets.
- The first step is understanding the structure of the Onionlink, where layers of encryption mask your identity and data from prying eyes.
- Sophisticated software tools are required to access these hidden networks, transforming ordinary data into an unreadable cipher.
- Within the depths of the Onionlink, you may encounter a vast array of content, from underground forums to leaked documents.
However, tread carefully. The lawless nature of the deep web attracts both criminals, making it a dangerous environment for the unwary.
Delving into the Labyrinth: A Guide to Onionlinks
Onionlinks, also known as shadow links, are like secret passages on the internet. They lead you to alternative corners of the web, often hidden behind layers of encryption and anonymity. To navigate these labyrinthine paths, you'll need a determined hand and an open mind. First, remember that onionlinks are often found on niche platforms or communities. Don't expect them to be listed in your usual search results.
- , you'll need a compatible application like Tor, which allows you to browse anonymously and securely.
- Be aware that the content behind onionlinks can be diverse. Exercise caution and critical thinking when exploring these uncharted territories.
Onionlinks offer a unique opportunity to discover hidden aspects of the internet. They can lead you to dissident communities, censored information, or even artistic expressions that wouldn't be found elsewhere. But remember, with great potential comes great responsibility. Always prioritize your onionlinks online safety.
Hidden Web Entry Anonymity: Surfing the Hidden Web Safely
Venturing into the hidden network requires a commitment to security. While Onionlink offers a layer of privacy, it's crucial to implement additional steps to reduce threats. A reputable VPN can further encrypt your connection, while utilizing sound cybersecurity habits is critical.
- Keep in mind that the hidden web can be a dangerous space, and exercise care when interactingwith users.
- Stay clear of sharing sensitive information unless you fully trust the recipient.
- Ensure your software is current to patch any security flaws that could be leveraged by threats.
By recognizing the inherent hazards and taking measures, you can surf the hidden web more securely.
Journey Through the World of Onionlinks
The realm of deep web links can be a intriguing place. It's a layer beyond the surface, bursting with stories just waiting to be explored. Navigating these digital mazes can be tricky, but for those adventurous enough, the rewards might be astounding.
- Prepare yourself for a unforgettable journey.
- Dive into the unknown depths of the onionlinks world.
Be warned though, as this digital frontier is not for the timid. It's a place where lines are crossed, and you never know whatyou might find.
Hidden Treasures: Finding Value in the Onionlink Network
The distributed nature of the Onionlink network often leads to overlooked treasures. While many concentrate their attention on more traditional platforms, savvy users are unearthing hidden potential within this unique ecosystem.
- From specialized communities to innovative projects, Onionlink offers a environment for individuals to connect in ways not possible elsewhere.
- By delving into this often ignored network, users can tap into a wealth of information and may profit.
Whether you're a seasoned copyright enthusiast or simply curious about the future of the internet, Onionlink presents an exciting opportunity to participate in something truly groundbreaking.
Delving into the Shadows of Onions: Hazards and Vulnerabilities of Onion Connections
While hidden internet hubs can offer a degree of anonymity and access to otherwise unavailable information, they also harbor a host of dangers. Users venturing into these shadowy realms run the risk of encountering cybercriminals, who may attempt to compromise security. Criminal operations are rife on onion networks, making it a breeding ground for deceptive tactics. Additionally, the inherent anonymity can embolden users to engage in cyberbullying, with little fear of accountability.
- Be cautious when accessing information on onion networks..
- Employ advanced security measures such as a VPN and unique passwords.
- Recognize the threats and withhold confidential information.
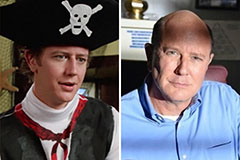 Judge Reinhold Then & Now!
Judge Reinhold Then & Now! Samantha Fox Then & Now!
Samantha Fox Then & Now! Mike Smith Then & Now!
Mike Smith Then & Now! Robin McGraw Then & Now!
Robin McGraw Then & Now! Sarah Michelle Gellar Then & Now!
Sarah Michelle Gellar Then & Now!